SIEMs….. what are they and why do we care?
A SIEM is a Security information and event management system…. still confused or not overly sure what it does. I made a simple info graphic.
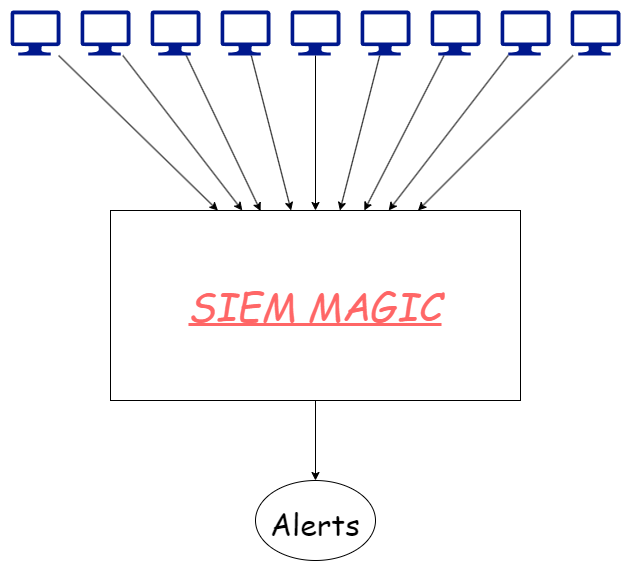
see? Magic.
Oh Magic isn’t enough for you? Ok, maybe we will delve into it a bit more……
What are they
A SIEM is generally known for holding logs for the environment, used to investigate and determine security incidents. Often it is overlooked that this system is valuable for other parts of the IT function within the company and thus you have large companies with multiple logging solutions.
“But why do we care in our lab” I hear you ask…… well why wouldn’t you want centralised logging? One of the purposes of this lab is deploy malware and get information on what it does. Another purpose is to develop my own rules and detection criteria. My skills in C are just not great, and by not great I mean basically non existent. So what better place to create alerts and detections than at the logging level. Yes this wont allow me to create preventions via this means but visibility into the activity is better than sitting around like a blind bat.
Choosing a SIEM solution for your lab
There are many SIEM solutions out there that would be useful, most popular would be Splunk and ELK. both have their advantages and give you different skills as you use them. One of the things that I needed to look at when evaluating a SIEM for my lab was cost. Whilst I’m happy to pay for some things like VMWare workstation Pro, the cost I was looking for here with a SIEM was FREE.

Additionally, I was looking for something I already had experience in setting up and funneling logs into. I have experience in both splunk and ELk and thus came to the conclusion that the free of those two would be the one I pick, spoiler alert…… I chose the open-source ELK.
Setting it up
If you want a guide on how to setup ELK in a standard way then there are heaps of tutorials out there, here are a few that look good to me.
- https://www.digitalocean.com/community/tutorials/how-to-install-elasticsearch-logstash-and-kibana-elastic-stack-on-ubuntu-20-04
- https://logz.io/learn/complete-guide-elk-stack/#installing-elk
But I followed the official one from Elastic here
Did you check that link before you clicked it? ![]()

Getting logs to the SIEM
The setup is basic but easy. Once the SIEM is setup you need to work on getting logs into it. Lucky for us, Elastic have an awesome tool for windows machines called “WinLogBeat”. Basically set the config and forget.
If you don’t want to do this on all machines, you can setup windows log forwarding on the workstations and forward the logs to a central location, then have them farmed off to ELk from there. In a larger and more secure environment this would be an optimal way of doing things and would reduce the hole that is punched through the firewall to get to the SIEM. But we dont have a large environment and I sure as hell don’t want it to be secure, where is the fun in that ![]()
“But Dan”, you may be asking, “what about the linux systems you’re running”…… Shush you im getting there. ![]()
Elastic have also released a tool called FileBeat…… who would have guess that this does the same thing for linux as it does for windows. Again an easy setup and set and forget.
Limiting storage
Limiting the retention time on logs will save us on space. The aim will be to keep 30 days worth of log, but how we do that is another question. I am still working this out and it will probably be a part of another blog post in the future once I am able to reliably manage log retention. so…… coming soon…… TM
Thats all for today, what are you still doing here, go read those how to guides and make your own SIEM for your own lab.
get.
go.
thx ok bai ![]()
